Smart Trust: The Rise of Blockchain in Edge Computing, Part II
 In part I of this series, we introduced blockchain as a potential answer to the questions of data security in the current trust economy. We summarized blockchain as a secure, trustworthy record-keeping process that makes the keepers safe too, as opposed to a system of trusted keepers who secure the process. It is sometimes referred to as a “ledger.”
In part I of this series, we introduced blockchain as a potential answer to the questions of data security in the current trust economy. We summarized blockchain as a secure, trustworthy record-keeping process that makes the keepers safe too, as opposed to a system of trusted keepers who secure the process. It is sometimes referred to as a “ledger.”
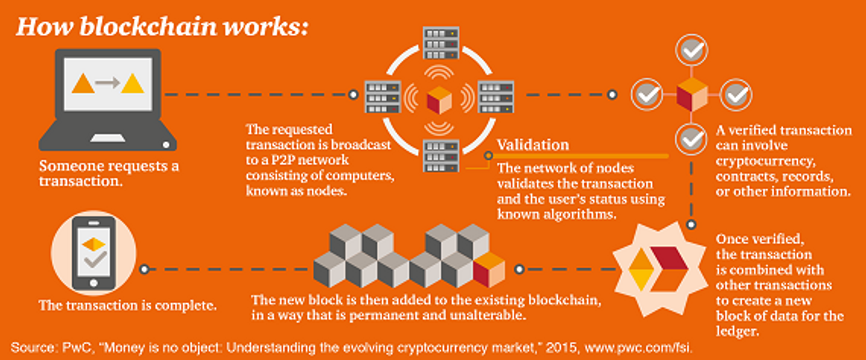
Blockchain employs a complicated system of computing to irreversibly and permanently store records and enact transactions. It works in conjunction with other cybersecurity measures like encryption, limited access and authorization to keep a network safe.
A block is a digital unit of records being stored, along with their values. One block contains one actionable record or fact, like a down payment for a house. The records in a blockchain can be anything: from monetary like Bitcoin, to contracts, signatures and licenses, such as Monegraph.
The chain is the sequence of all the blocks, hence the term blockchain. The ledger will never be contradictory because the chain cannot accept blocks that precede the previous block logically. For example, if Block A says I owe you $500 and I try to submit Block C that says I fulfilled the loan without recording a Block B payment, my block will be rejected.
The system gets its computational power from being on a peer-to-peer (P2P) network between servers and computers, like an internet. Member machines are referred to as nodes. Each node simultaneously stores the blockchain, validates records and has the option to add to the blockchain. Members of the P2P network are anonymous to their peers and not inherently trustworthy. However, because it is so difficult to defraud the system – one must own 51% of the machines in the network – anyone can participate with confidence.
Members must pay in to participate, attaching values to their facts. Members verify other records and submit their information to the ledger. For a member’s fact to go into the chain, a consensus, or 51% of the network, must agree that it can be added. Once approved, peers must go through difficult mathematical challenges, combing through massive number sets and problems, to add the verified block. Nodes that search for verified facts and add them are called miners and they receive the value of the block as compensation. Once a miner adds a block on its chain, that record is pushed out and stored on every node in the exact same sequence, permanently.
The system prevents fraud and unauthorized access. Machines outside of the network cannot access the chain. Machines inside the network cannot change the ledger unless 51% of their peers agree, which is unlikely. The information within the blocks are also encrypted, which means miners and nodes do not know the content of the facts. Because the blockchain is simultaneously stored on every machine in the network, there is a permanent record of all transactions and operations. It also removes excess steps in authorization systems and reduces risks created by vulnerabilities.
Part III of our series will talk about this painstaking system of recording and storage can be applicable to edge computing, banking and other high-risk digitized operations.
Check out this video from PCMag that illustrates blockchain.
Categories:
